What the team is usually trying to fix
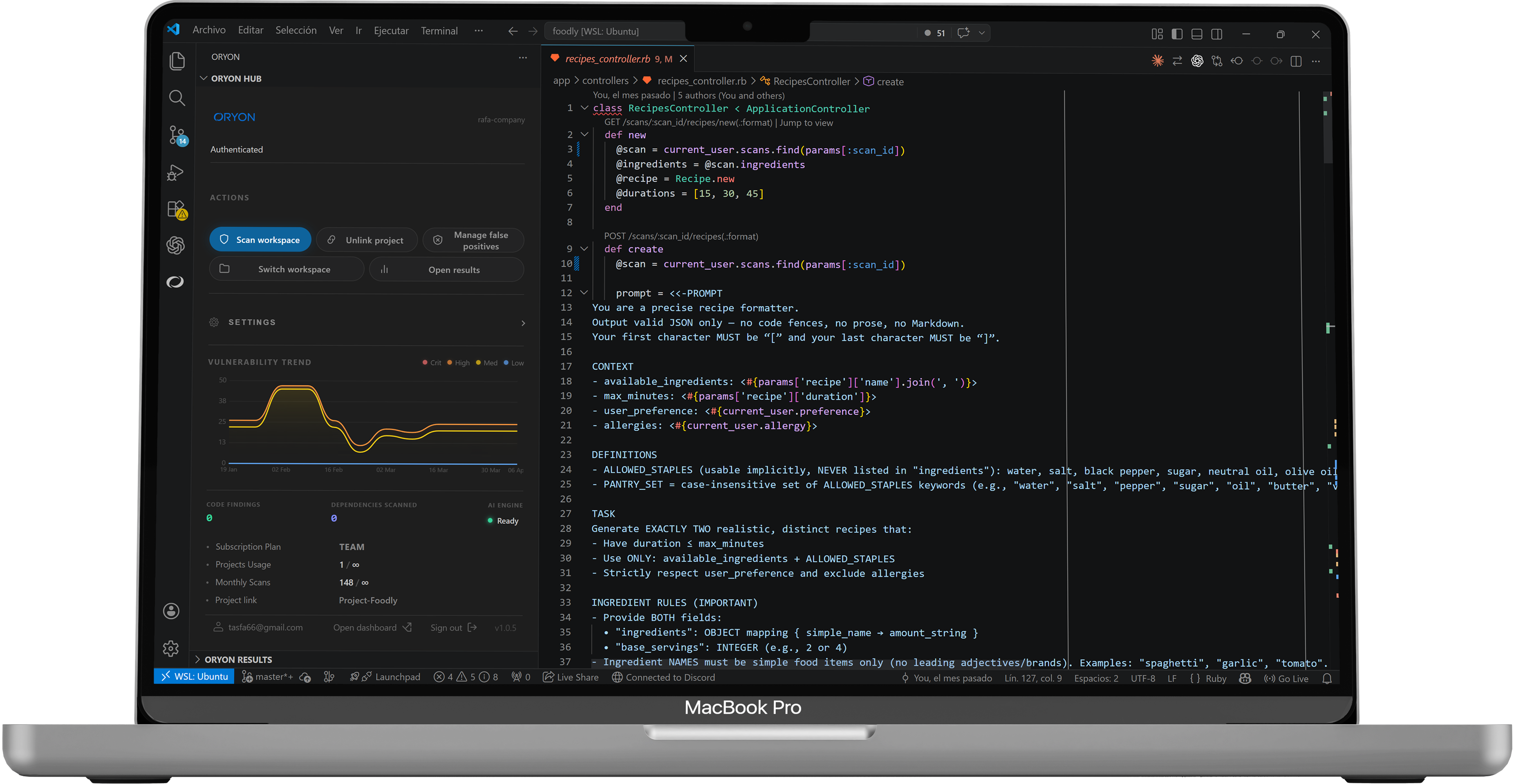
- Security feedback arrives too late, after CI or review cycles have already become expensive.
- Developers lose trust because the tool generates too much noise and not enough context.
- The team wants repository history and shared suppressions without making the cloud the scanning engine.